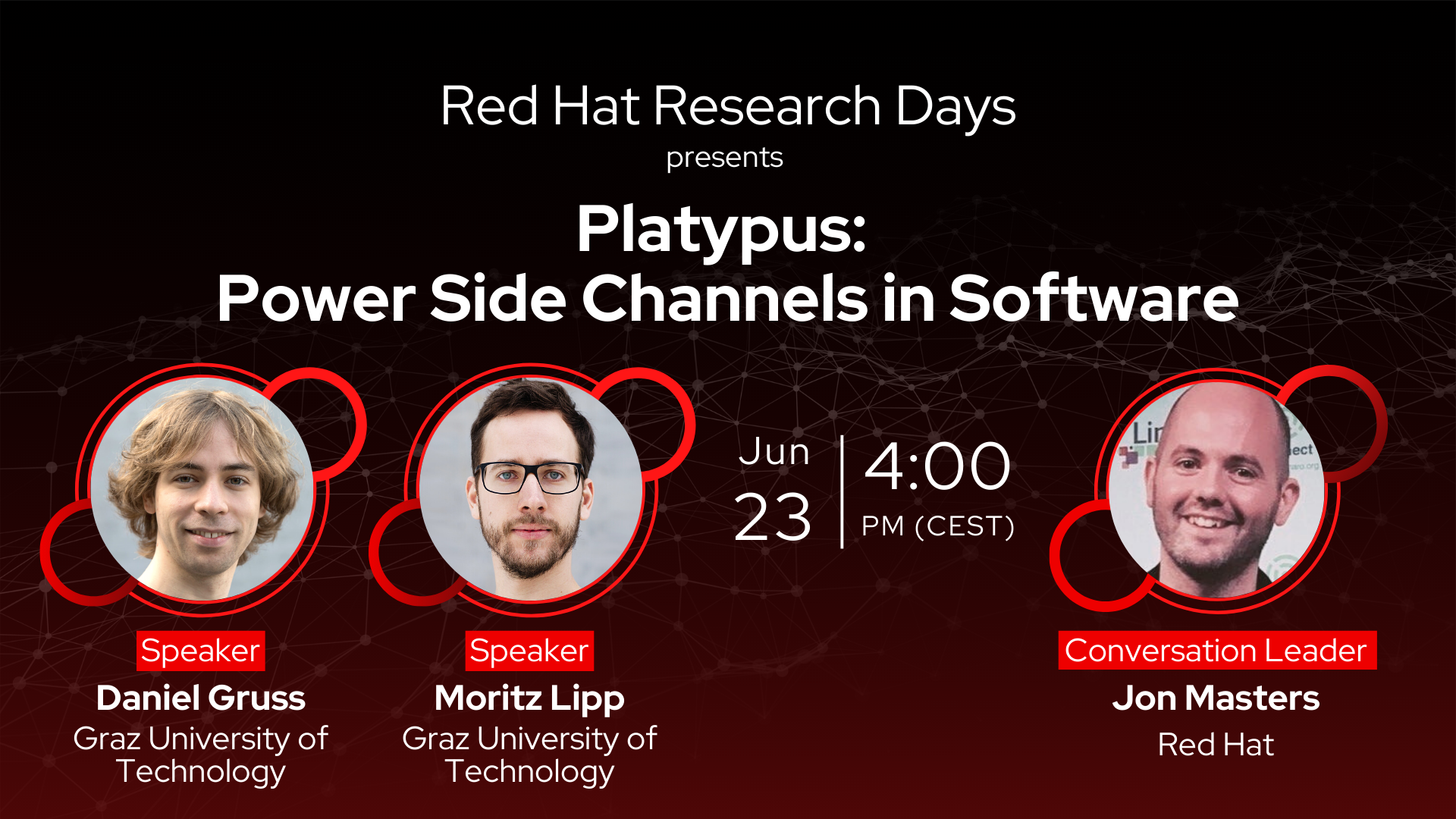
Platypus: Power Side Channels in Software
June’s event in the Red Hat Research Days monthly series focused on side-channel attacks featured by security researchers from Graz University of Technology. TU Graz computer scientists Daniel Gruss and Moritz Lipp will present Platypus attacks: a method that allows power side-channel attacks even without physical access. The whole session was accompanied by a live interactive discussion led by Jon Masters, creator of the Red Hat Arm and microprocessor side-channel security vulnerability mitigation efforts.
Abstract
In this talk, we will demonstrate how we can attack modern processors purely in software, using techniques from classical power side-channel attacks. We explain how we abuse the unprivileged access to energy-monitoring features of modern Intel and AMD CPUs. With Platypus, we show how to steal cryptographic keys from the operating system or trusted-execution environments, and how to break kernel address-space layout randomization within seconds. Finally, we discuss the mitigations that prevent our attacks.
Speakers
Daniel Gruss, Assistant Professor at Graz University of Technology
Moritz Lipp, University Assistant and PhD candidate at Graz University of Technology.
Conversation Leader
Jon Masters, Computer Architect and Distinguished Engineer at Red Hat
Session recording