Red Hat Research Quarterly
Open source cybersecurity and the next generation of computer scientists

Article featured in
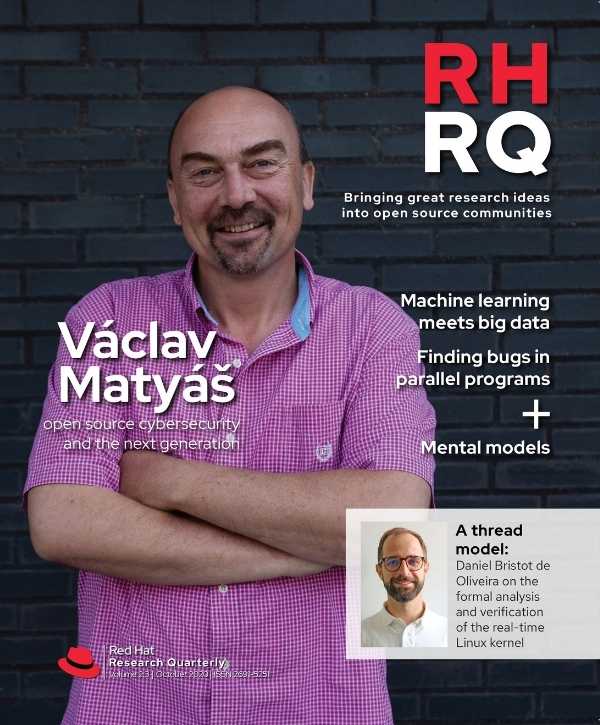
Red Hat Research Quarterly invited Mike Bursell, Red Hat’s Chief Security Architect, to chat with Václav Matyáš, Professor with the Centre for Research on Cryptography and Security at the Faculty of Informatics, Masaryk University, about his focus on cybersecurity education and how he has leveraged open source software projects as the laboratories and proving grounds for his students’ work.
Mike Bursell: First of all, tell me about how you got involved with open source.
Václav Matyáš: That’s a good question, and it goes well over ten years back in history. In the Faculty of Informatics [at Masaryk University], while working ad hoc with various industrial partners in Brno, we decided to put some form and coherent structure to our industry cooperation. So we surveyed the town, and since we had been keen on open source since our establishment, twenty-five years back, we found the most natural vibe with what we were doing and thinking in Red Hat.
We thought, okay, Red Hat is the place to discuss more systematic and even wider cooperation. We found the people that were keen to discuss it, like [Red Hat engineer] Radek Vokál and others, and it made sense, it fit, and it started working.
Mike Bursell: Excellent. Twenty-five years of open source, that’s a long time. Is that open source commitment a decision that your faculty made, or the university made?
“We wanted to see the software working, wherever it was possible, and we wanted to get feedback with respect to that software.”
Václav Matyáš: Another good question, and I don’t know the answer. I can only speculate, and my speculation would be that it was in the blood and ideas that we started the faculty with, twenty-five years back. I was a PhD student then, and we always tried to have the publications open. We wanted to see the software working, wherever it was possible, and we wanted to get feedback with respect to that software.
Mike Bursell: You got involved with open source as a PhD student, or even before that?
Václav Matyáš: During my PhD studies. There were many more people within the Faculty of Informatics then that were already contributors to open source. I was just a user and observer.
Mike Bursell: It wasn’t on my list of questions, but I’m very interested in open source and security, specifically. Do you have any strong feelings about the position of open source and security, or maybe the other way around, security and open source?
Václav Matyáš: I do. I have a very funny story. There is a small association of industrial players that is hosted by the university, and it tries to play some role in cybersecurity education at secondary schools. They came out with a publication, a few weeks back, where they took a position that basically dates to the previous century: “open source is not reliable because nobody is supporting it, and you cannot really trust it, so therefore it should not be used for security purposes.” When I read that, I thought—okay, this must have been written by somebody who still wears the same glasses as in the 1990s.
So today we had a very nice discussion with a couple folks from the town, and also from Prague, on openness, confidentiality, and open source—not only open source software, but also open hardware. It was very useful for us, because many of the discussions went back to factors that were true deep in the last century.
“I am definitely a keen promoter of open insight into security solutions.”
Today the situation is like this: You have an algorithm, mathematically proven, sound under various constraints, okay, nice, but then there is some logic with which you implement it, maybe even in some dedicated hardware. Then come the questions: Where did the hardware come from, what are the impossible vectors in that, what do you know about that hardware? Then you realize that you know much less about the hardware than you know about most of the software. Why would you scrutinize software so much in terms of algorithmic complexity, maybe even performance, and look at it from various angles, security being one of them, before you say okay, this software is good enough to run, but then you run it on hardware about which you know nothing? I am definitely a keen promoter of open insight into security solutions.
Mike Bursell: I was looking through some of the work you’ve been doing on your academic page, and I noticed a piece of work you did on the usability of OpenSSL. Tell me a bit about that, and why that’s important.
Václav Matyáš: We came to that about four years back when we realized that OpenSSL has got well over twenty years of history, but for people who don’t use it every day, there’s much too much to learn just to do basically primitive functions.
From that we thought, okay, let’s examine this systematically. This was an area that started booming about ten years back, with end users and usability. We thought, everybody does that, so let’s look at this from a different angle. We have users of the library that are developers and skilled IT folks, and we tell them to use OpenSSL for this and that. So they are using this famous security library. Then we’d measure what they like about it, what they don’t like, what is easy to do. We did the first evaluations, and then we figured out that the scope was too broad, so we narrowed it down to the work with public e-certificates. Even just that will be a pretty good PhD thesis.
My student, Martin Ukrop—I believe he has an article in the last issue of RHRQ (https://research.redhat.com/research-quarterly-2-2, “Don’t Blame The Developers” — Ed.)—was a very good and natural pick to be the PhD working on this, and with him we designed the experiments. Of course, after the experiment, you will not only learn the results, but you will learn everything you did badly in designing the experiment, how it should be better next time. We repeat this in basically annual cycles.
Mike Bursell: It’s not just how you create certificates, but how you use them and how they’re trusted. Could you talk a bit about that? Because it underpins so much of what we do on the internet these days.
Václav Matyáš: Definitely. Certificates have been around for about two decades, but still a majority of people who are using them and relying on them misunderstand what they are good for, and how they work. Our experiments showed this clearly, even with the skilled people who are IT pros. They don’t understand what the OpenSSL system is telling them about why a particular certificate is good for this, and not good for that. We realized it’s actually a lot of stuff that goes beyond code, to documentation error messages.
Most of the research that we did in the past three years is now public, and it went through some nice publications. Now we’re working on another, which will be Martin Ukrop’s final paper, that shows our effort and improvements we did to redesign error messages and redesign documentation. We actually have very nice support from Red Hat staff. So the last paper will be showing positive outcomes: not only what the problems are with SSL, but what we could improve, what we did improve, and where we still feel some debt to the project. We did not have the power to finalize the improvements, and we hope other people can follow up.
Mike Bursell: Do you often work with Red Hat when you find these sorts of things where improvements could be made? Obviously you’re interested in not just pointing out problems but improving security. How do you work with Red Hat, and what other routes do you take in the faculty?
Václav Matyáš: Why and where with Red Hat? One reason is open source: we want to see the improvements happening, and as much any academician we want to see things working and be published.
With some companies that takes years. For me as a researcher, on one hand it’s positive, on the other hand frustrating to give someone an idea that they don’t implement, then four years later they decide that it’s a very good thing and they use it in another project later on. Whereas in open source, you can see whether the thing is useful right now, and we can actually go forward and help.
We are not afraid of coding, so when we see that things can be adjusted in this way or that way, we can do that. With a company that has proprietary software, sometimes even under NDA for both sides, we cannot make this step forward. From this perspective, our work with Red Hat fills these academic expectations, and makes us happier to work with projects that are open source.
Mike Bursell: For me this is how open source should work. It’s contributing not just code, but knowing you can contribute code, and audit code, and test, and make sure that the ideas and the theories are also all in there. I love how that fits at several layers.
I was looking at the other work you’ve done in crypto primitives. Could you talk about that?
“Even if we do not know exactly how they run things we can watch the output, so we then became obsessed with watching output.”
Václav Matyáš: This comes from a series of projects that we had, both with the Czech National Security Agency of that time, and industrial partners. We found that we often work with computer systems, typically small hardware like smart cards, where we cannot check what they actually run, but we can observe through various side channels how they run things, whether they run things one way or another. Even if we do not know exactly how they run things we can watch the output, so we then became obsessed with watching output. We got a crazy idea: okay, we do not know how these designers of these hardware pieces—not just smart cards—do that, but let’s have these things running for weeks in clusters, and let’s generate millions of keys out of that.
We later repeated the same effort with the crypto libraries, where it was much easier, but the inspiration came from closed hardware. Then we thought if we generate these millions of keys— it was actually tens of millions of keys ultimately—then we can run various checks, look for patterns. We figured out some things that were not expected at all: where people expected some particular data, particular components, or cryptographic keys to be random, we were able to show visually and numerically that clearly these are not random.
Mike Bursell: Explain to people who may not technically know as much about security why that’s important, why the randomness of these things is important?
Václav Matyáš: It’s important for a very simple reason. If you see somebody tossing a coin, and you see five times head, head, head, head, what do you expect the sixth attempt?
The mathematician will tell you the likelihood is still one-to-one. The naive person will tell you it’s definitely going to be a tail. And the security person will tell you it’s a biased coin, so it’s definitely going to be a head again. You have the same situation, three different backgrounds, and three different answers to the question. The importance in security is best explained like so: Imagine that someone could choose a key that was created now or at any time in the past, and your goal is to determine when the key was created. If you have no clue, and the chances of the key being created now or 50 million years ago are the same, then it’s impossible to determine the time of the key generation. However, if it’s not really random and the chances are not the same—for example you know that it has been generated today—then you definitely will not be guessing for the previous millions and tens of millions of years. You have a much more narrow subset of choices to make, and your chances to win this bet and find the right key are much higher.
Mike Bursell: The bet is basically that they can decrypt when you send your credit card to an online retailer, and they can maybe get your credit card because they have enough information to bet or to guess when it was encrypted?
Václav Matyáš: Exactly. It ties also to the non-crypto system security. If I have an unlimited number of guesses that only cost me some computing time, then I will try all the possible time expressions for today, and I will do what we call brute force it. If I know the key has been generated today, I can definitely guess the time if I’m not extremely limited in my number of choices.
But if the entire universe of time expressions was available …
Mike Bursell: You’d be guessing for a long time.
Václav Matyáš: I can’t do it.
Mike Bursell: Yes. Excellent. I wanted to talk about another thing, which I understand you’re interested in, which is girls and women in tech. What do you do there?
Václav Matyáš: It’s a loss of human talent, I would say. I’ve got three kids, and one of them is a girl, or a woman now. I can see that when it comes to elementary school, and then sometimes even unfortunately high school, girls get the message, “Mathematics is not exactly for you, and computers, no, this is not for you at all. You will definitely find other subjects where you will excel better.”
Making these statements just based on sex is, a) of course, unfair, but b) it’s harming the entire human population, because from my experience women and girls have been successful in coding, successful in proposing computer systems, successful in history in running computer systems. Look at the World War II examples. I see no natural constraint that would make me claim there is some area of computer science where women are systematically worse than men.
“If we deprive ourselves of this different look at the matter, then we are losing.”
I believe, given the different treatment of women in many ways, that at the age of productivity, after high school or university, the mindsets of women will be somewhat different than the mindsets of men, in some aspects. I’m generalizing now a lot, I understand, but having a different angle and different view of the problem helps a lot, particularly in security. If we deprive ourselves of this different look at the matter, then we are losing. We can have an attacker that may say, let’s have this group of people like women—or another group—looking into this, and they will see the mistake that we did, that we missed.
Mike Bursell: Indeed. I agree, this is very important. What does your faculty do? Do you do anything with Red Hat to encourage women and girls?
Václav Matyáš: I believe that I can say that we try to do a lot. Out of the universities in the wide region of the Czech Republic, when speaking of similar faculties or schools, our numbers are impressive, but still not impressive enough for me. I mean we are now around 20 percent—sometimes we go to 22 percent, sometimes 19 percent—but around 20 percent of our intake to programs are women. This is better than other technical computer science and engineering faculties in the region, but it still can be improved significantly.
We hosted for many years the association that is fairly well known in Czech and Slovak Republics, Czechitas, the young ladies that actually have their primary mission to increase the number of women that are engaged in IT. Now they’ve gone to bigger offices than we can provide, but still we host a lot of their seminars. I was with them for some discussions just last week, when they had some trainings at our university, and we tried to cooperate with them as much as possible. We are meeting Red Hatters at these occasions quite a lot, actually, so thanks a lot to Red Hat for that.
Mike Bursell: If I were a person who’s not got a security background—I might be an undergraduate, I might be someone looking at moving in IT to something different—but I’m interested in security, where would you say I should start? Are there any books, are there any things I should read, are there any films I should watch?
Václav Matyáš: If it’s a university student already, then I would say grab a copy of Ross Andersen’s Building Distributed Systems book. For that you need the person to understand the basics of computer systems, and appreciate some factors of everyday life. This is not a book that I would recommend to a high school student, by any means.
For a high school student, then it actually depends. We do a lot of things with talented high school students, but these are students that were selected typically by their teachers of computer systems, or they came to computer science from discussions with their parents or something. They already believe that computers are something that is maybe good for their future career. For these people, we already treat them nearly the same way as we do university students. We give them very specific tasks, we provide them with more guidance how to get to the solution, but still we do not provide much of a narrative how or why to do security.
Whereas, if we have discussions with general student groups in various high schools who are not these selected highly talented students, I would suggest probably another book where a lot of stories and interesting ideas come from, and it’s tied to history: The Code Book from Simon Singh. These students will typically not be up to reading David Kahn. Giving them David Kahn is a very good option, but some may not read a book that thick. Singh is much shorter, and serves this purpose well.
Mike Bursell: I agree, it’s a very good book. I sometimes tell people if they’re looking for fiction and they want a big book then Cryptonomicon is a fascinating introduction to the world of how people think about it. There’s lots of stuff about World War II and modern things as well, but it’s a fun read, so that’s another place I start.
Václav Matyáš: That’s a very good read, too. You are right.
Mike Bursell: Can you give me some examples of the things that you’re doing in the faculty at the moment that you might point someone at?
Václav Matyáš: One of the things is a set of tools. It ties to the crypto primitives and helps one to check whether the crypto primitives, whether in hardware or software, have been implemented correctly. We have been redesigning many of them for quite a few years, providing them of course as open source and supporting them as well. This is definitely something that we believe in. The ultimate expectation is that you will have a semi-automated system to which you can give an implementation, whether in software and maybe in the future hardware as well, and it will not only tell you whether the functionality, let’s say output of cryptography, is wrong or right, but if it’s wrong it will give you a few hints as to what may have been the causes.
“It will probably take a decade or two, but I believe that in the future these will be the first steps of cryptoanalysis.”
This is challenging. It will probably take a decade or two, but I believe that in the future these will be the first steps of cryptoanalysis. The way we do cryptoanalysis now, we do various tests, then we check the outputs with NIST and so on. In the future we are running pieces of software, and there is already enough knowledge to see that not only we run pieces of software, but that software—if we have reached enough data—tells us that there has been something fishy, and maybe why it has been fishy.
Mike Bursell: Yep, yep.
Václav Matyáš: So that’s one. Another is the one we already discussed, and that’s usable security. There we can document for the student, “This is the problem with public e-certificates, about which we told you about in class. These are the experiments that we did—you can easily read about them—and this is what we do now improving error messages.” It’s not just looking out of the window and just by the weather deciding how to redesign it; there is some systematic effort that we learn from psychologists how to work with people, how to experiment, and how to get to a better version. Similarly, I’ll go through about three or four other areas.
Mike Bursell: Another question I was going to ask is, let’s assume that I’m a talented MA student, or undergraduate student, and I come to you and ask which areas are going to be important in security in the next ten to twenty years? Which subjects would you say will be really interesting?
Václav Matyáš: That’s a good question. We usually are very pragmatic. I mean you have two sorts of people. One sort comes with their idea and their problem already, and you have to nurture them, help them.
For example: We have a new PhD student that will be supported by Red Hat, starting in September. When I first met him about four or five years ago, he was an undergrad student, first year, and he came with a very interesting challenge. He said, “I am from this city in Slovakia, from Žilina, and we managed to break into their transport ticketing system. We reported the problems to them, and what we heard back was threatening by lawyers, and that we should not disclose this error to anybody.”
I told him okay, I will help, but you have to pay for it, and you have to pay by working on the problem, describing it in detail, considering other angles and variants of the attacks, and documenting it. I took this student for a graduate course, where he wrote this report, and then we provided the report to the city transport company, giving them two months’ leeway to have their problems fixed before the report goes public. As a report of a student it enjoys academic freedom under our laws, so it could be made public. Two months’ time was more than sufficient to fix these mistakes, and by supporting this student in that particular scope of work, he now enjoys a lot of things that we do in the lab, and now he’s working on other things that we already see as very good prospects for the future.
The other type of student just comes with open hands, and asks the way that you asked me. Then we say okay, we have these projects that we are running in the lab, and by running them it means that we are spending our effort on them, and that means that we believe that they will be useful. You see us and our people with whom we work at the university spending our time on this, so we suggest that you consider one of these things that we are doing.
SHARE THIS ARTICLE
More like this
It is by now well understood that we humans are capable of creating systems that are more complex than we can understand.
Since the inception of artificial intelligence research, computer scientists have aimed to devise machines that think and learn like human beings. What else could AI do?
Thoughts on open source and open collaboration from the Greater Boston Research Interest Group (RIG).
Research at Devconf.us: Optimizing and automating the foundations of computing.
Parallelism promises to make programs faster, yet it also opens many new pitfalls and makes testing programs much harder.
To design effectively for our users, we need to learn more about them. If we don’t, we may make a product that our users can’t be efficient in, or worse, a product that our users have no need for in the first place.
The recent advances in AI and telecommunications are enabling a new set of complex cyber-physical systems, including those for safety-critical applications.
I have been spending a lot of time lately thinking about all the hard problems involved in managing large-scale systems. Why? Well, it turns out to be a really important topic for Red Hat Research and for the Red Hat engineering community that we hope to serve.
Like so many other events this year, DevConf.cz is going virtual from February 18-20. Originally an internal Red Hat event held in Brno in the Czech Republic, this free, volunteer-organized event is now in its thirteenth year and is open to all.