Preventing Rust Programs From Becoming C Programs
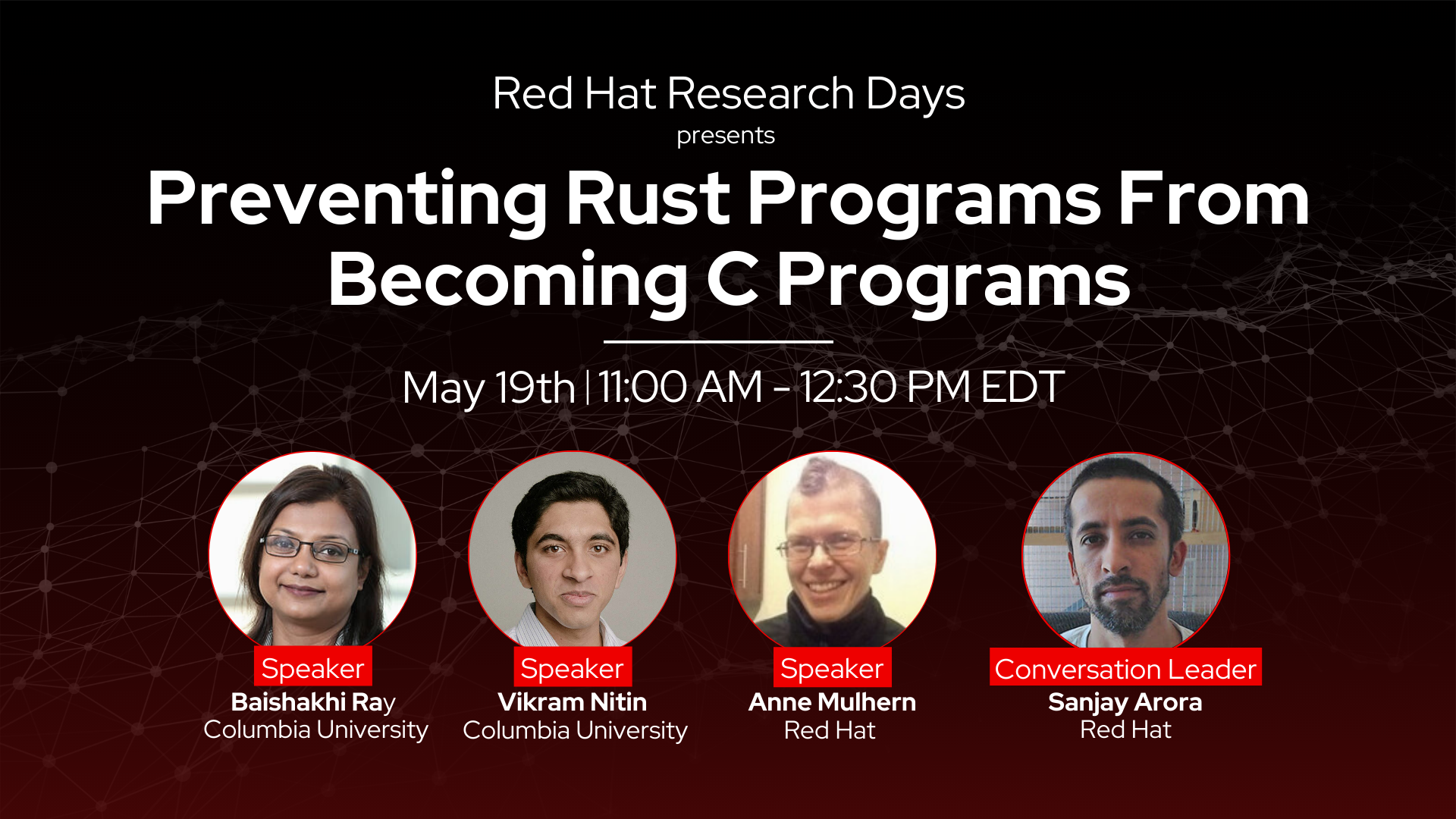
Join Red Hat Research for the next Research Days event, “Preventing Rust Programs From Becoming C Programs” on May 19, 2022 from 11AM to 12:30PM EDT (5PM CEST, 6PM IDT).
This talk will help developers using Rust for memory safety find and avoid subtle issues that can lead to unsafe behavior in programs. Baishakhi Ray, Associate Professor, Columbia University, Vikram Nitin, Columbia University, and Anne Mulhern, Principal Software Engineer, Red Hat will explain different types of memory safety vulnerabilities that can arise in Rust programs and present their ongoing work on automated detection of these vulnerabilities. Sanjay Arora, Data Scientist, Red Hat, will lead the conversation, which attendees are welcome to join live.
Abstract
In comparison to C, the Rust language provides significant memory safety guarantees through its concept of lifetimes and its borrow-checker. However, Rust has an “unsafe” keyword which suspends some of the compiler’s safety checks within a specified code block. Such unsafe code destroys the guarantees of a program written in pure Rust, and it becomes the responsibility of the developers to ensure the memory safety of the unsafe code. For example, a function that internally uses the unsafe code should still have the same memory safety guarantees as a function written in pure Rust. If the function is not implemented correctly, then those who use this function may write code that is vulnerable to memory safety errors, even though the code that they write is pure Rust.
In this presentation, we explain different types of memory safety vulnerabilities that can arise in Rust programs and present our ongoing work on automated detection of these vulnerabilities.
Speakers
Baishakhi Ray, Associate Professor, Columbia University
Vikram Nitin, PhD Candidate, Columbia University
Anne Mulhern, Principal Software Engineer, Red Hat
Conversation Leader
Sanjay Arora, Data Scientist, Red Hat
Session Recording and Materials