Suppose I came to you and told you that your front door had a cheap deadbolt that could be opened with a credit card, and that lots of people who want to rob you would soon know about it. You’d probably thank me very much for the information as you left for the hardware store to buy a better lock.
On the other hand, suppose I told you that deadbolts aren’t all that helpful anyway, because people who really want to get into a house can break a window or kick in the door. You’d probably say, well, that’s a risk I can live with, and tell me not to be such a worrier.
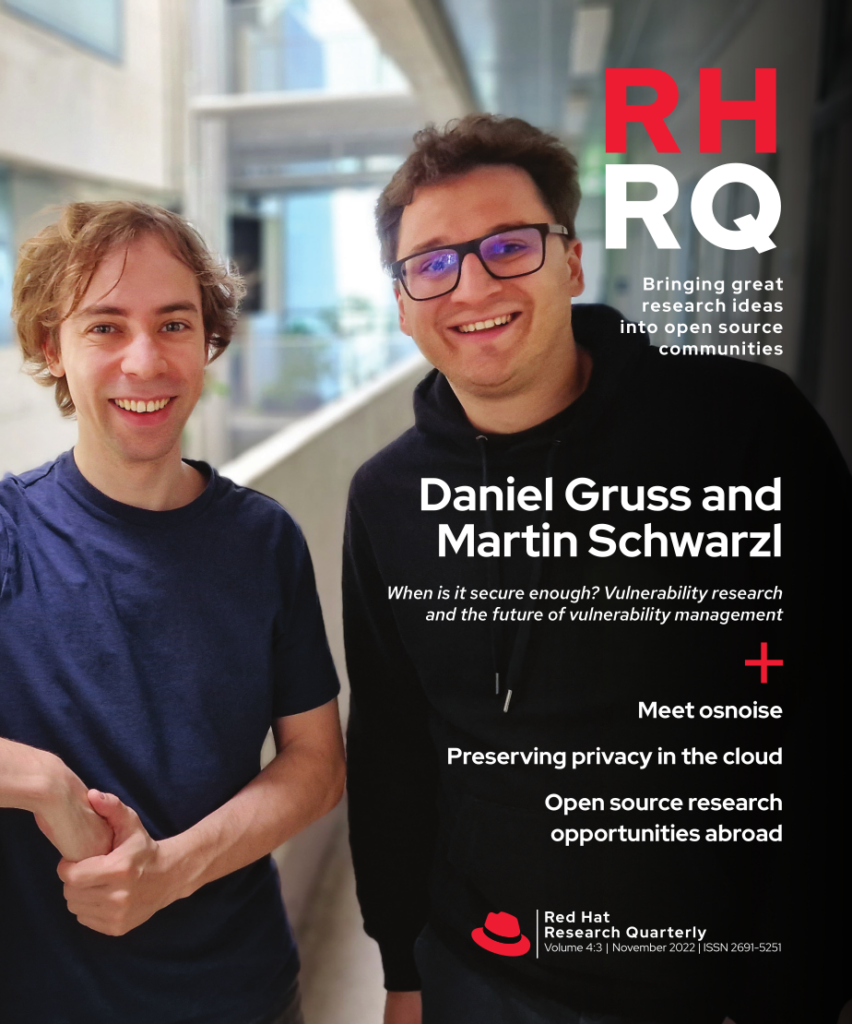
We make this same trade-off every day in computer security, and understanding the nuances around it—which vulnerabilities are really worth fixing, which ones aren’t, how do we assess the difference—is a huge part of the work Daniel Gruss does every day. Gruss, the first researcher to appear twice on the cover of this magazine, spends his days as a security researcher at TU Graz in Austria trying to find security holes and figure out how to plug them, if they are worth plugging. He and his student Martin Schwarzl talk with Red Hat Vice President of Product Security Vincent Danen in this issue about the trade-offs they have to make when deciding where to spend their time as researchers. They also discuss the similar tradeoffs hardware and software makers must make to deliver products that are secure enough, but not so secure that you can’t use them for anything. I finished the interview more convinced than ever that open source is a vital part of mitigating these problems, and I’m encouraged to see hardware and software makers moving in that direction too.
Encryption is a big part of making things secure, of course. This issue features an in-depth look at Fully Homomorphic Encryption: the set of techniques one can use to encrypt information such that it can still be computed on, without the party doing the computation being able to interpret the results. This sounds entirely impossible to me, but in fact with sufficient computing time it is possible to do things like addition and multiplication on encrypted data without knowing the decrypted inputs or outputs of the computation. Until recently, this kind of computing has been so time consuming that it is impractical for any real-world use. Researchers at Boston University, however, have found that using an FPGA programmed specifically for these computations can make the work so much more efficient that it might, with certain caveats, become practical in the real world. Why would you want to do this? Read Red Hatter Lily Sturmann and BU PhD candidate Rashmi Agrawal’s piece on the technique to find out.
Finally, I am very happy to share that we are featuring another piece by Linux kernel developer Daniel Bristot de Oliveira in this issue, this one on ways of identifying and reducing noise in kernel processing to maintain real-time consistency guarantees. Daniel has a special talent for describing very advanced techniques in a way that even non-kernel-developers like me can understand, and I’m delighted to have his continuing contributions to the magazine as the Linux kernel expands into the exotic domains where real-time safety must be guaranteed. Daniel’s work exemplifies what happens when open source research meets open source practice, and I’m proud that RHRQ can showcase that connection.