RHRQ asked Lily Sturmann, a senior software engineer at Red Hat in the Office of the CTO in Emerging Technologies, to look back at the past few years of research in the area of security and privacy research and share her perspective on the future. She has contributed frequently to the Red Hat Next blog, and her most recent article for RHRQ was “Preserving privacy in the cloud: speeding up homomorphic encryption with custom hardware” (Nov 2022).
Security and privacy have moved further to the forefront of technical concerns over the past several years, as more organizations make use of hybrid cloud environments encompassing machines and devices on-premises, on-cloud infrastructure, and at the edge. The reliability of cryptographically backed integrity and confidentiality guarantees on infrastructure owned by third parties is critical for those running sensitive workloads in these environments, and cloud providers have responded by making technologies like confidential computing and trusted platform modules (TPMs) available on their infrastructure.
Open source through the research lens
As RHRQ starts its fifth year it’s impossible to resist the temptation to look back at all we’ve done so far. The result is this collection of perspectives. Together they paint an inspiring picture of the innovative work that can be accomplished when engineering know-how and bold research questions come together in open source environments.
- Focus on open hardware, Ulrich Drepper and Ahmed Sanaullah
- Focus on clouds and research IT, Heidi Picher Dempsey and Gagan Kumar
- Focus on testing and operations, Daniel Bristot de Oliveira and Bandan Das
- Focus on AI and machine learning, Sanjay Arora and Marek Grác
- Focus on education, Sarah Coghlan and Matej Hrušovský
Similarly, the privacy challenges involved with interorganizational collaboration and computation on large, sensitive data sets have motivated innovative work on multiparty computation and fully homomorphic encryption. Throughout its history, RHRQ has highlighted the strides made by researchers in these privacy-enabling fields, as in an interview with Harvard researchers James Honaker and Mercè Crosas (Aug 2020) on making open source solutions for storing and sharing richly detailed information about experiments, software, and systems more available to all.

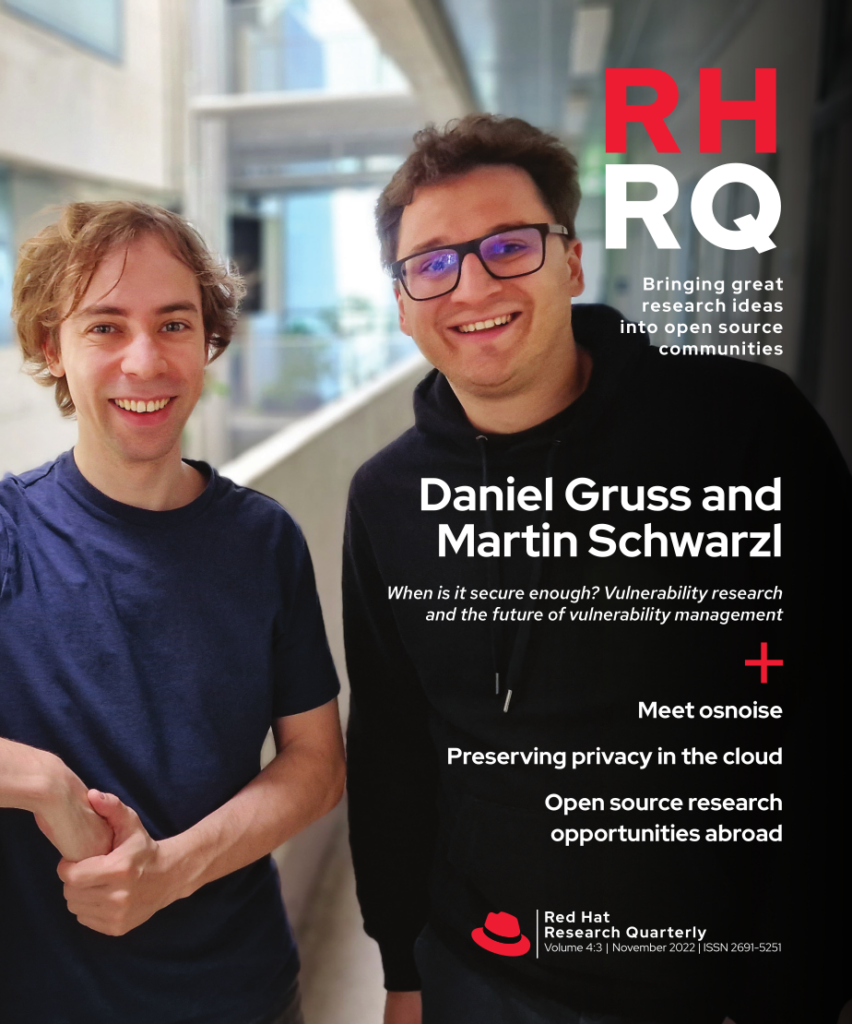
RHRQ’s very first issue in May 2019 featured the work of side-channel attack researcher Daniel Gruss of Graz University of Technology (Austria). With Research Director Hugh Brock, Daniel wrote about “Taking a proactive and holistic approach to cybersecurity.” Calling for a more vibrant exchange between security researchers and engineers, Daniel discussed Spectre and Meltdown, two CPU vulnerabilities that brought attention to the widespread practice of viewing security only at the level of individual components. Daniel and collaborator Martin Schwarzl were featured again in an interview with Red Hat Vice President of Product Security Vincent Danen. “When is it secure enough?” (Nov 2022) elaborated on the importance of taking a system-wide view of security, especially at the intersection of software and hardware. Daniel and Martin’s latest research on side-channel attacks is introduced in the “Research project updates” section of this issue.
Another critical area is supply chain security in software, as demonstrated by the series of Executive Orders from the US government. This is especially apt with the high-profile vulnerabilities and attacks related to software dependencies that have been manifesting ever more frequently, the most notable being the vulnerability in Log4j discovered in 2021. Masaryk University PhD candidate Agáta Kružíková’s article on “User authentication for open source developers” (Aug 2021) in public open source repositories describes one of the many challenges in the complex software supply chains that we all depend on. The Sigstore project has gained recognition for helping to make signatures in the open source software supply chain standard practice, with the first-ever Sigstorecon held in 2022 as a co-located event at KubeCon Detroit.
Looking ahead, we will continue to face challenges like the growing power of quantum computing and Shor’s algorithm potentially making much of the cryptography we rely on today obsolete. But we also have many new engineering tools available, from wider adoption of the security-oriented Rust programming language to WebAssembly to the novel ways we can protect code and data integrity and confidentiality across heterogeneous environments. While security is by definition a constantly evolving field, the power of open source software and open research to meet these challenges and create opportunities remains constant.